Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
#1 Best Pitch for Smoking Hot Tech
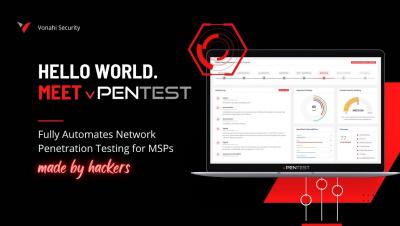
On July 21st, Vonahi Security won 1st place against 7 other innovative companies in Channel Program’s monthly Pitch Event. Each company had exactly 7-minutes to pitch their product or service to the channel. Over 450 MSP attendees feasted their eyes on some hot new tech. At the end of each pitch, attendees had about two minutes to fill out a survey and vote for their favorite pitch.
Why MSPs Love vPenTest - Automated Pentesting Platform
Vonahi Interview with Jenny
2022 Challenger Interview: Vonahi Security + Decipher Cyber
Respect in Security
Vonahi Security, as a member of the cybersecurity community committed to the prevention of all forms of harassment within our industry, hereby pledges its support for a workplace and community free from harassment and fear.
SrClient DLL Hijacking: a Windows Server 2012 0-day that won't be patched
I recently discovered that all versions of Windows Server 2012 (but not Server 2012 R2) are affected by a DLL hijacking vulnerability that can be exploited for privilege escalation. Moreover, the flaw can be triggered by a regular user and does not require a system reboot. Sounds like a pretty big deal, right? Well, not according to Microsoft, unfortunately.
What's in a (re)name: RCE Hunting in CMSs via Unrestricted File Upload
During a recent bug hunting binge I discovered my first two vulnerabilities that could be exploited to achieve remote code execution (RCE). No bragging rights were earned though, because finding and exploiting these issues was incredibly straightforward. I’m not humble bragging here (I wish). In fact, the issue underlying both vulnerabilities, which each affect a different content management system (CMS), is very basic and was literally the second thing I checked for.
When the PATH to SYSTEM is wide open: Philips SmartControl DLL hijacking (CVE-2020-7360)
Remember that high school teacher who was never more than one chapter ahead of their students? Well that is me, in this blog. ¯\_(ツ)_/¯