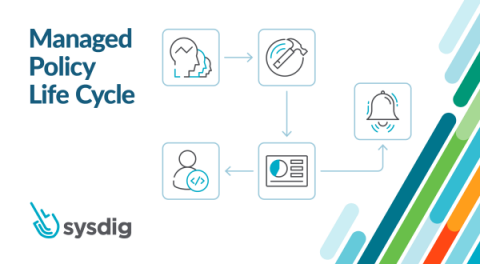
Prioritize Alerts and Findings with Sysdig Secure
If you work in Security or Operations, you are surely familiar with the concept of “alert fatigue.” Alert fatigue Syndrome is the feeling of becoming desensitized to alerts, causing you to potentially ignore or minimize risks and harming your capability to respond adequately to potential security threats.