Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
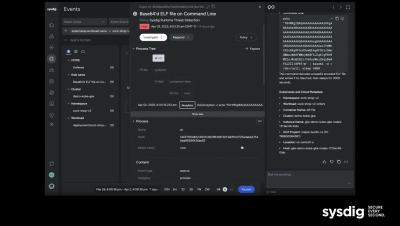
Sysdig Sage Demo
Learn how to get up and running with Sysdig Sage in only a few minutes!
AI-driven CSPM: How GenAI will transform Cloud security posture management
Generative AI (GenAI) is poised to revolutionize the cloud security posture management (CSPM) space, bringing intelligence, automation, and context to increase the effectiveness of managing cloud risk. Maintaining a robust security posture in the cloud can be challenging as the number of deployed cloud services increases across diverse clouds. Soon, AI-driven CSPM will play a critical role in helping security and cloud teams to keep pace with misconfigurations and compliance gaps.
The evolution of the Sysdig Agent
For the past six years, I’ve had the unique privilege of contributing to and witnessing the evolution of Sysdig Agent. As a Technical Writer, I create educational content that helps Sysdig customers get the most value out of it. The Sysdig Agent, which began as a simple sniffer probing system calls, has transformed into a powerful defender of cyber threats and vulnerabilities, safeguarding workloads across regions—and even underwater in submarines! How cool is that?
tj-actions/changed-files with Falco Actions
A compromise (CVE-2025-30066) was discovered in the popular GitHub Action tj-actions/changed-files on March 14, 2025. It impacted tens of thousands of repositories that use this action to track file changes. This blog will explain how Falco Actions can easily be integrated into your workflows to help detect this CI/CD attack and provide in-depth visibility. Falco Actions is an open-source project that monitors your CI/CD workflows for potential threats in real time, leveraging the OSS tool Falco.
Sysdig and Google SecOps: Unifying cloud security for SOC teams
In our first blog post, “Sysdig Secure-Google Chronicle integration – Why, what, and how“, we introduced the idea of connecting both platforms, highlighting their complementary strengths and providing a high-level overview. Now, we’re taking it a step further—moving beyond theory to focus on practical, real-world applications.
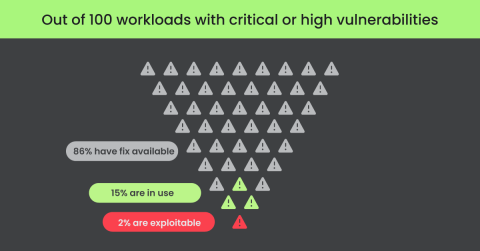
Next-Gen Container Security: Why Cloud Context Matters
Container security has experienced significant transformation over the past decade. From the emergence of foundational tools like Docker to the maturation of orchestration platforms such as Kubernetes, the container security landscape looks different than it did even a few years ago. With Gartner predicting 95% of organizations will be running containerized applications in production by 2028, it’s clear that container security is going to be a key priority for most organizations moving forward.
Measure what matters: 5 benchmarks every security leader should track
Are you looking to validate if your cloud services are resilient and adequately secured? Consider the following five cloud security benchmarks to assess your organization’s cloud deployments. CISOs know that their security programs should be data-driven and that metrics are integral to communicating the status of security capabilities to organizational stakeholders, including the executive leadership team and the board of directors.