Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
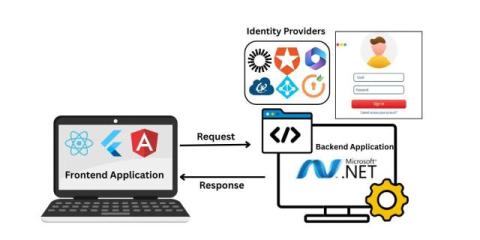
Secure Your Decoupled .NET Apps with SAML SSO
The Power of Video Capture with VisioForge Video Capture SDK for .NET
ASP.Net Hosting for SaaS Platforms: Challenges and Solutions
Preventing SQL injection in C# with Entity Framework
Best Practices for Cybersecurity in .NET Applications
Securing Samba Ports: Essential Practices for Safeguarding Your Network
.NET developers alert: Moq NuGET package exfiltrates user emails from git
On August 8, 2023, the.NET community was informed that the testing library called Moq exfiltrates developer's emails from their development machine and sends them off to third-party remote servers. Snyk has already published a security advisory and will alert developers who scan and monitor their.NET projects with Snyk.
New .NET Malware "WhiteSnake" Targets Python Developers, Uses Tor for C&C Communication
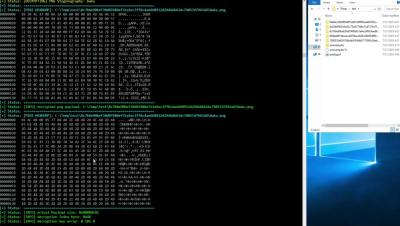
The JFrog Security Research team recently discovered a new malware payload in the PyPI repository, written in C#. This is uncommon since PyPI is primarily a repository for Python packages, and its codebase consists mostly of Python code, or natively compiled libraries used by Python programs. This finding raised our concerns about the potential for cross-language malware attacks.
Attackers are starting to target .NET developers with malicious-code NuGet packages
Malicious packages are often spread by the open source NPM and PyPI package repositories, with few other repositories affected. Specifically – there was no public evidence of severe malicious activity in the NuGet repository other than spam packages used for spreading phishing links. As with other repositories, the JFrog Security Research team regularly monitors the NuGet repository for malicious packages, including manual analysis of suspicious code.