Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
How to Write Your First Rules in Rego, the Policy Language for OPA
Rego is the purpose-built declarative policy language that supports Open Policy Agent (OPA). It’s used to write policy that is easy to read and easy to write. Fundamentally, Rego inspects and transforms data in structured documents, allowing OPA to make policy decisions. Rego was originally inspired by Datalog, a common query language with a decades-long history, but extends its capabilities to support structured document models like JSON.
What's new in Calico Enterprise 3.14: WAF, Calico CNI on AKS, and support for RKE2
At Tigera, we strive to innovate at every opportunity thrown at us and deliver what you need! We have listened to what users ask and today we are excited to announce the early preview of Calico Enterprise 3.14. From new capabilities to product supportability and extending partnerships with our trusted partners, let’s take a look at some of the new features in this release.
Enabling Self-Service Recovery in a Multi-Tenant Kubernetes Environment with CloudCasa and Capsule
Detecting and mitigating CVE-2022-26134: Zero day at Atlassian Confluence
A new zero day vulnerability actively exploited in the wild has been found in Atlassian Confluence. The vulnerability CVE-2022-26134 affects all supported versions of Confluence Server and Confluence Data Center allowing an unauthenticated user to run arbitrary commands remotely. The Atlassian team confirmed the vulnerability with an official tweet and then also published a security advisory to update its customers.
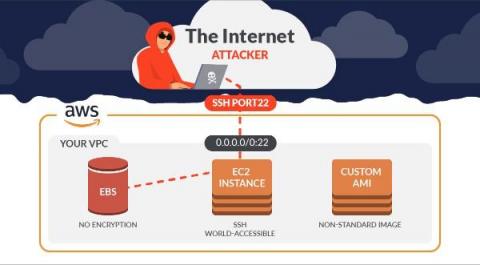
How to Secure Amazon EC2 with Sysdig
Elastic Compute Cloud (EC2) is arguably one of the most popular AWS services, and really needs no introduction but here is one anyway. With Sysdig, you can secure EC2 by managing configuration and permissions risk, meeting compliance requirements, and managing vulnerabilities on containers and host VMs. When it comes to EC2 and Hosts themselves, Sysdig Secure alerts us in multiple ways.
KubeCon EU 2022 - Trends & Highlights
Kubecon EU returned to Spain. This time to Valencia, city of paella and horchata and, of course, a great place for big events. We had a great time meeting you all in person, and attending the talks. Here are our hot takes from the event. The main event started on Wednesday, but before that different co-located events took place: Ebpf Day, Cloud Native SecurityCon, and PrometheusDay among others. These events gathered a large number of attendees.
How to use Atomic Red Team to test Falco rules in K8s
The best way to know if something works is to try it out. Ensuring that your security products are actually working is a fundamental task of routine maintenance. This is why it is so useful to use tools like Atomic Red Team that generate suspicious events based on ATT&CK techniques and see how Falco triggers alerts. In this blog, we will cover how to install and run the Atomic Red Team environment on a Kubernetes system for testing Falco rules.
Using Teleport to Secure SSH and Kubernetes Access
OPA Design Patterns: Offline Configuration Authorization
An OPA design pattern, as detailed in a previous post, gives you an architectural solution to solve one or more common policy problems. In this blog post, we describe what we call the Offline Configuration Authorization design pattern for OPA. Remember that each OPA design patterns covers the following information.