Hunting with Elastic Security: Detecting covert data exfiltration
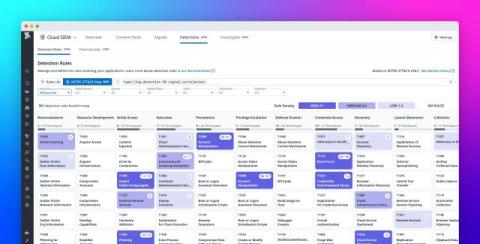
Not all network traffic is what it seems. Some flows conceal secrets, quietly exfiltrating sensitive data beyond your defenses. MITRE ATT&CK T1048 - Exfiltration Over Alternative Protocol is a stealth technique adversaries use to smuggle data out of your environment by bypassing traditional security controls.