A Practical Guide for Becoming a SOC Analyst
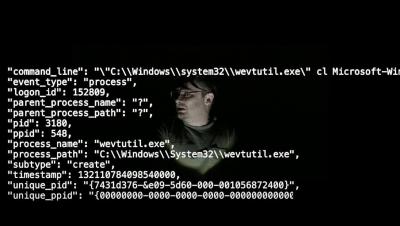
Practical Experience is important in getting cybersecurity work, and a home lab is a great option, but how do you do this for a SOC Analyst or cyber defender lab? Eric Capuano of Recon Infosec spells it out in a blog post. In this video, Dr. Gerald Auger shows you exactly why this Home SOC lab will give you an incredible advantage in learning practical cybersecurity skills.