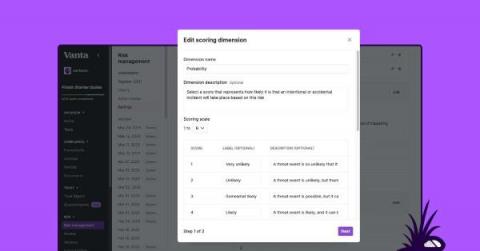
Improve your risk posture: Introducing Risk Management customization
Today we’re excited to announce Risk Management customization, a collection of new capabilities in our platform that enhance the existing Risk Management solution and give you more flexibility to enable custom risk management scoring and prioritization. Currently in beta, Risk Management customization will be generally available in the coming months.