Can Manufacturing Defects Really Compromise Your Network's Data?
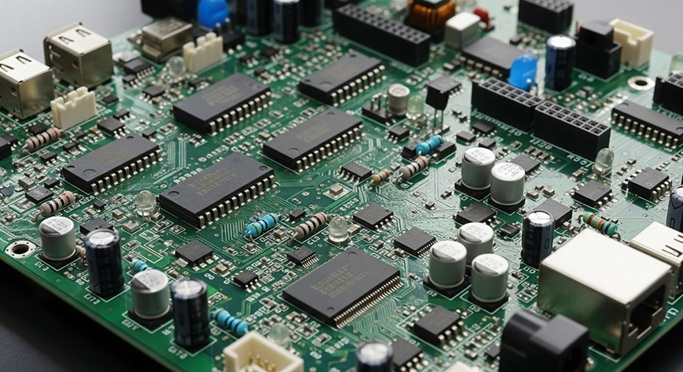
Whenever we consider network security, it tends to cross our mind that we are dealing with hackers, malware or poor passwords. However, there is a less conspicuous danger that never makes the news: the physical elements that constitute your network infrastructure. In particular, the printed circuit boards (PCBs) that drive your routers, switches, and servers may have manufacturing defects that open holes in your security that you never thought of.
It is almost paranoid in the beginning. What impact could such a minute defect on a circuit board have on something as intangible as data protection? The fact of the matter is more problematic than most IT experts will admit, and it is worth learning how these physical flaws can be translated into severe security threats.
The Hidden Connection Between Hardware Flaws and Data Vulnerability
Consider a PCB as the nervous system of any network device. It is used to direct electrical signals, power distribution and to ensure proper communication between all the components. The defect that appeared in the manufacturing, be it a microscopic crack in a trace, a soldered joint, or a contamination of the board material does not necessarily lead to instant failure.
Rather, these vices are usually intermittent issues. Under some temperature conditions a hairline fracture can lead to signal degradation. A cold solder joint could perform well on most occasions but it will fail randomly when the board is flexed or becomes hot. Such unpredictable behaviors are especially risky since they are difficult to diagnose and can take the form of data-compromising manifestation.
Examples of Hardware-Induced Risks:
- Corrupt Packets: These can pass a broken network switch undetected.
- Weakened Encryption: Unstable voltage regulation caused by a faulty power circuit would result in weakened keys by the encryption modules.
- Authentication Failure: Authentication may fail unnoticed, and access points expose themselves to short periods of failure.
When Quality Control Fails: Real-World Implications
Not every manufacturer of PCBs can meet the same standards. Defective boards may make it to the market due to cost-cutting, time-crunch production schedules, or insufficient test procedures. The thing is that such defects cannot always be seen on the first deployment.
The administrator of a network may install what seemingly is well-operating equipment only to realize after several months that he or she has been experiencing random cases of data corruption. At that point, sensitive data may have been leaked, backups may have corrupted data or security logs may be incomplete because of temporary failures.
Quality standards can also depend on the geographic location of manufacturing. Working with a reputable PCB manufacturer in France often means adhering to strict European quality regulations and environmental standards that indirectly improve product reliability. These manufacturers usually have strict testing measures such as thermal cycling, electrical testing, and visual inspection measures that ensure that defects are detected before boards are shipped.
Types of Manufacturing Defects That Create Security Risks
Not every defect is equally dangerous to the data security, yet there are certain categories that should be given attention.
1. Trace Defects
Trace defects are those defects which are formed when the copper pathways which transport signals are not formed properly. This may be breaks, shorts or impedance mismatches. Even a small trace issue in high-speed network equipment can result in signal reflection, timing errors or data corruption, which may go unnoticed by security systems.
2. Soldering Problems
Components that are not attached to the board correctly can lose contact at random. Suppose there is a security chip that randomly goes dead during milliseconds, not quite long enough to miss a verification step, but not long enough to cause an error alarm.
3. Material Contamination
Conductive particles that are introduced due to material contamination may form undesired circuits. Such routes may not result in direct failure but may permit signals to escape between circuits that are not supposed to be connected, and may allow encrypted data to be vulnerable to side-channel attacks.
4. Dimensional Inconsistencies
The dimensional inconsistencies influence the ways boards fit into their housings. Inappropriate fit may cause mechanical loading, bending and ultimate failure of components. In network equipment that processes sensitive information, such failures may turn on security settings before more noticeable failures are detected.
Geographic Factors in PCB Sourcing
The source of your network hardware is more important than you may think. The regulatory environment, labour practices and quality assurance traditions are different in different regions.
- The EU Framework: A PCB manufacturer in Portugal operates within the EU framework, which includes RoHS compliance, REACH regulations, and generally strong worker protections that correlate with attention to detail. These manufacturer might be providing to the needs of industrial, medical, and aerospace industries for which the security-for-reliability standards satisfying anything from basic equipment to "critical infrastructure" are due.
- Unsupervised Production: On the other hand, boards made in plant with little supervision may pass the basic functional test with hidden flaws. These issues usually do not manifest themselves until devices can be used in the real world with different temperatures, humidity, and electrical noise.
New Markets and Quality Variability
Turkey has emerged as a very significant force in the production of electronic equipment and many of these plants are able to give competitive prices and enhance their capability. A reputable PCB manufacturer in Turkey might deliver excellent quality, particularly newer facilities equipped with modern equipment and implementing international standards.
Nonetheless, like any manufacturing zone, due diligence counts. There may be a wide gap between the best-practice facilities and those that are cutting corners. In the case of network infrastructure where data security is the most important factor, it will be crucial to fully vet suppliers, irrespective of the location.
Protecting Your Network from Manufacturing Vulnerabilities
Well what are you supposed to do about this? You are not going to look under the microscope at every circuit board before installing it.
- Supplier Selection: Begin with the choice of suppliers. Select manufacturers that have documented quality systems, and preferably have certification to quality standards such as ISO 9001, IPC-A-600 or industry specific certification. Order test reports and inquire about failure rates statistics of similar products.
- Inspection Processes: Introduce incoming inspection processes, however simple. Visual inspections will be able to identify blatant issues. More advanced companies may apply electrical testing or x-ray inspection to the essential parts.
- Behavior Monitoring: Observation of deployed equipment in case of abnormal behavior possibly of hardware issues. Periodic failures, random crashes, or poor reliability might be indicative of defects in manufacturing, prior to causing security breaches.
- Hardware Diversity: Lastly, have diversity in hardware of critical systems. Do not buy all the equipment of one manufacturer or production lot. This reduces the effect in case a systematic fault is found out later.
The Bottom Line
A network hardware defect is a real but manageable threat to the security of the data. Although they are not as dramatic as a sophisticated cyber attack, they may result in vulnerabilities that are more difficult to notice and respond to. Your network has a physical basis that should receive an equivalent level of attention to your software protection, firewall regulations and access policies.

