Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Seamless path to Zero Trust for Texas: Lookout Receives TX-RAMP Level 2 Certification
Here at Lookout we have a long tradition of supporting the cybersecurity requirements of all levels of government in the U.S. This is why I’m thrilled to announce that we have received a Level 2 certification, the highest tier of authorization, from the Texas Risk and Authorization Management Program (TX-RAMP).
What is Lockdown Mode for iOS and iPadOS and why should I care?
Apple recently announced a new feature in its upcoming iOS and iPadOS called Lockdown Mode. The aim is to protect users such as corporate executives, government officials, journalists, activists and other users that are likely targets of sophisticated surveillanceware. The goal of Lockdown Mode is to restrict certain device capabilities that spyware has exploited in the past in order to reduce the attack surface on Apple devices.
5 Misconceptions about DAST for Mobile
Organizations that develop mobile apps need to be aware of the potential cyber security threats. These threats can lead to the loss of users' private data, which can have serious repercussions for industries like fintech, healthcare, ecommerce, etc. In order to prevent these malicious practices, Dynamic Application Security Testing (DAST), a security testing tool, has been introduced. It helps to weed out specific vulnerabilities in web applications whenever they run in the production phase.
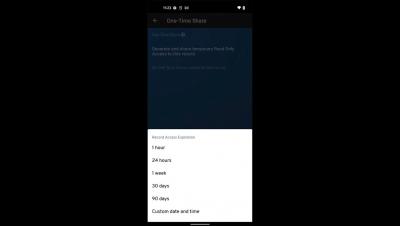
Keeper for Android on Google Play
Your Ultimate Social Media Security Checklist [2022 Updated]
Social media is both a boon and a bane. While it has connected billions of people, made them more accessible, and created more possibilities for the end-users. There's no doubt that it has also made them more susceptible to security threats and vulnerabilities. According to We Are Social, there are around 4.62 billion active social media users worldwide. This is precisely the very reason why cyber criminals love social media as well.