Fireside Chat With TPRA: Three Hard TruthsAbout TPRM in the Post-Mythos Era
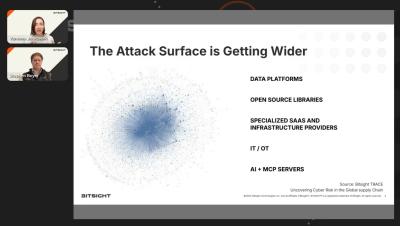
Frontier AI models like Mythos have intensified the urgency to rethink cybersecurity. But for third-party risk teams, the harder question remains: how do we prioritize the actions that actually drive business outcomes? As TPRM becomes more tightly tied to business impact, resilience, continuity, and revenue protection, leaders need a clearer view of the hard truths shaping their programs.