What does Sysdig do?
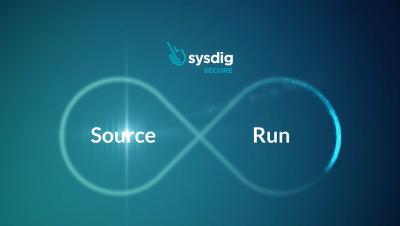
What does #Sysdig do and how is it different from other cloud and container security tools? Hear CEO Suresh Vasudevan explain how Sysdig can help customers secure and monitor their containers on the cloud from source to runtime. Stay up to date on the latest cloud native news and trends, get all the info on latest vulnerabilities and discover new ways for securing and monitoring kubernetes and containers on our blog.