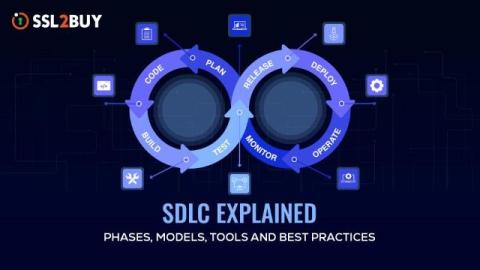
Software Development Life Cycle & Its Role in Modern Systems
As software systems grow more complex, managing the development process becomes mandatory. The Software Development Life Cycle provides a structured standard that helps teams build, test, and maintain reliable applications.