Building a hybrid data fabric for integrated security
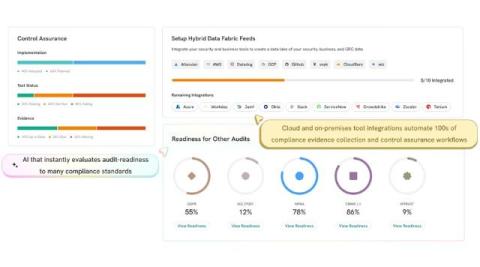
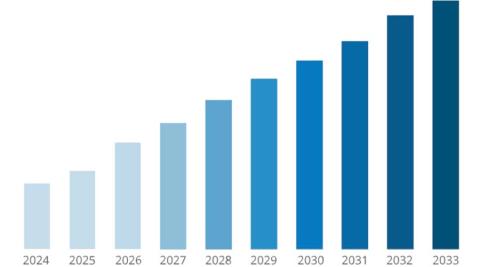
Organizations face increasingly complex security challenges driven by the convergence of on-premises environments, cloud deployments, and edge computing nodes. The implementation of a hybrid data fabric has emerged as a powerful approach for managing and integrating data across distributed architectures while ensuring robust, integrated security. This article provides a deep dive into the technical and strategic aspects of constructing such a fabric.