Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Keeper Security Named Winner for Encryption in 2023 Fortress Cybersecurity Awards
We at Keeper Security are proud to announce that we’ve been recognized by the 2023 Fortress Cybersecurity Awards as the overall winner for Encryption. The Business Intelligence Group conducts the annual Fortress Cybersecurity Awards to recognize experts, engineers, people and products in the field of cybersecurity.
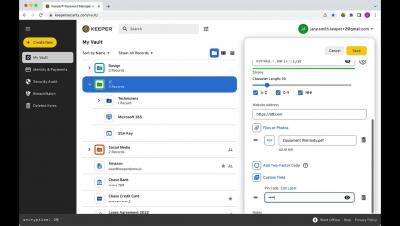
How To Use a Password Manager
How you use a password manager varies slightly depending on which password manager you have. However, they all have similar functionality. To use a password manager, you first have to set your master password, set up your multi-factor authentication methods, export and import your current passwords, download the necessary apps and create new strong passwords for each of your accounts.
What Is the Safest Way To Send Sensitive Documents?
Sending sensitive information over the internet is often necessary, despite the risks. You may need to send copies of your passport to validate your employment status at a new job, or you might need to send tax forms with your social security number to your accountant. How can you send this information without making it vulnerable to cybercriminals? Using a software platform that uses zero-knowledge encryption is the most secure way to share sensitive information and files.
What is Doxxing?
Doxxing, also spelled doxing, is when a threat actor publishes Personally Identifiable Information (PII) about their target online. This can include publishing the target’s place of employment, home address, credit or debit card numbers and any other sensitive information. The purpose of the threat actor publishing another person’s PII varies, but most commonly has to do with harassment.
How to Secure Your PayPal and Venmo Accounts
PayPal and Venmo are online platforms that let businesses and individuals send and receive payments. You can secure your PayPal or Venmo account by using a strong password, setting up Multi-Factor Authentication (MFA) and using other security features available. Since these accounts handle financial transactions and sensitive information, they are common targets for cyberattacks.
How to Make Your Email More Secure
You use your email address for a wide variety of things such as when you’re shopping or setting up an online account. Because your email is linked to so many different accounts, securing it is crucial to keeping your other accounts safe, since most password resets are sent to your email address. To make your email more secure you should create a strong password, enable MFA and always log out of your account.
Making the Business Case for PAM Deployment
Privileged Access Management (PAM) solutions are designed to protect organizations from a variety of threats that target privileged accounts, credentials and access. These solutions help to secure, manage and monitor access to critical systems and sensitive data.
How a Password Manager Enhances Productivity
People who don’t have a password manager often struggle with forgetting their passwords and having to reset them when attempting to log in to their online accounts. This is frustrating, time-consuming and leads to a loss in productivity. A password manager enhances your productivity since it remembers passwords for you, aids you in generating strong passwords and autofills your login credentials, saving you time to focus on more important tasks.
Cyber Threats Facing the Accounting Industry
Accounting firms handle sensitive client data on a daily basis, making them prime targets for cybercrime. According to PwC, accounting firms have a 30% higher risk of cyberattacks than other businesses. Breaches in the industry are among the most expensive, with IBM’s “Cost of a Data Breach 2022” report finding the average breach totaled $5.97 million.
Is Privileged Access Management Important for SMBs?
Yes, Privileged Access Management (PAM) is important for Small and Medium-Sized Businesses (SMBs). Any business that has privileged systems and accounts to secure and manage needs a PAM solution. Without a PAM solution in place, businesses are at a greater risk of suffering a cyberattack which can be financially and reputationally devastating. Continue reading to learn more about privileged access management and how it benefits SMBs.
The Pros and Cons of a VPN
The primary benefit of a Virtual Private Network (VPN) is that it keeps your information and identity private when using the internet to access sites or servers, download files and more. This is especially important when handling sensitive information on public networks, like checking your bank account at the airport or accessing work files remotely. There are a number of use cases, from personal device security to maintaining safe business networks, which we will cover in this article.
Going Glocal with Data Hosting
Customers of software vendors with multiple global data centers can more easily comply with regional data protection and privacy requirements by hosting their data in their preferred geographic region.
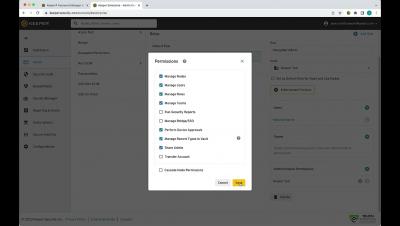
Keeper for Teams and Small Business 3 Minute Demo
What Is PAM in Cybersecurity?
Privileged Access Management (PAM) in cybersecurity is how organizations manage and secure access to highly sensitive accounts, systems and data. Without PAM, organizations are at greater risk of a cyberattack impacting privileged accounts. Continue reading to learn more about PAM and its crucial role in cybersecurity.
Cybersecurity Girl's tips for a strong password #shorts
What is a Hardware Security Key and How Does It Work?
A hardware security key, also known as a security key, is a physical form of authentication that provides you with access to systems, applications and accounts. Hardware security keys are often used as a second form of authentication or as a Multi-Factor Authentication (MFA) method. Read on to learn more about hardware security keys and the advantages and disadvantages of using them.
Keeper: An Essential Zero-Trust and Zero-Knowledge Cybersecurity Platform for the Federal Government
The U.S. federal government tends to move very slowly – except when it comes to zero-trust cybersecurity. The drive to get all agencies to zero trust is cruising along at warp speed, as evidenced by White House Executive Order 14028, CISA’s Zero Trust Maturity Model, OMB OMB M-22-09 and the DoD zero trust strategy and roadmap, all of which were released within the span of less than two years.
2FA vs MFA: What's the Difference?
The main difference between 2FA and MFA is that 2FA requires you to use one authentication method in addition to your username and password, whereas MFA requires one or more additional authentication methods to your username and password. Read on to learn more about 2FA and MFA, and how they differ from one another.
Keeping Data and Systems Secure With Privileged Access Management
Research shows that most of today’s cyberattacks occur when a cybercriminal gains access to a system through stolen credentials. Users with extra privileges, particularly IT administrators, are often targeted by threat actors who steal those privileges to access sensitive information and take control of systems. With an increase in virtual and hybrid work, across both the public and private sectors, these kinds of attacks are only becoming more common.
End-User Vault for Business & Enterprise
Employer Liability for Data Breaches: What Companies Should Know
Organizations are increasingly being held liable for breaches of employee data. But employers can take steps to mitigate the likelihood and impact of breaches. Any organization using an electronic payroll and benefits system stores and processes sensitive employee data — which covers just about every organization in operation today. There are many risks related to a cyberattack that compromises employee data, including legal liability, business interruption and reputational damage.
How Secure Are Password Managers?
Most password managers are very secure and safe to use. Depending on the password manager in question, some offer more security than others. To fully understand the security of password managers you’ll first have to understand what a password manager is.
What is SaaS? Hint: It Doesn't Mean "Cloud"
The U.S. federal government is committed to implementing zero-trust cybersecurity across all government agencies. In 2021, the White House issued Executive Order (EO) 14028, directing federal agencies to adopt zero-trust network architectures. A few months later, CISA followed up with a draft Zero Trust Maturity Model.