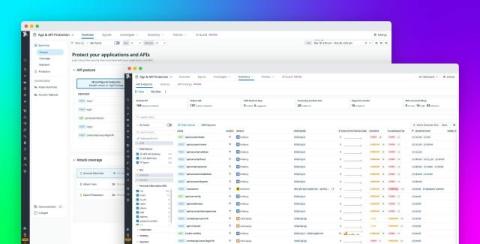
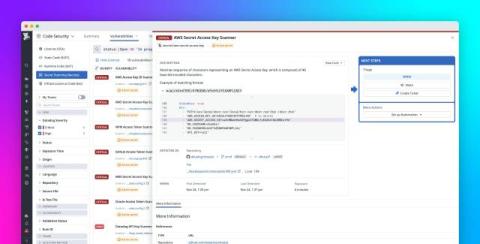
From discovery to defense: Securing APIs with Datadog App and API Protection
APIs now sit at the center of almost every digital product, from mobile apps and SaaS platforms to embedded services. As organizations scale, the number of endpoints grows quickly, as does the attack surface. Unmonitored or misconfigured APIs have already led to major incidents across industries, including data exposure, broken authentication, and large-scale account takeover.