Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Vulnerability scanning tools: What are they and how should they be used?
Part of the challenge of creating a robust security posture is collecting the right toolbox full of tools and services. There’s a wide world out there full of tools that can enhance your security, but one of the most productive types of tools every organization needs is a vulnerability scanning tool. To help you navigate these types of tools and recognize how they fit into your information security system, we’re taking a closer look at these tools and how they work.
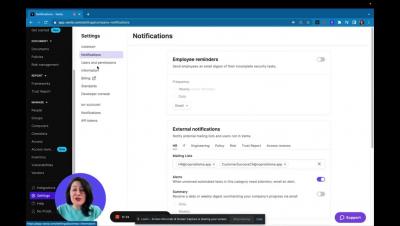
Vanta
New in Vanta | January 2023
It’s been a busy start of the year for Vanta. We’ve made some major additions and improvements, such as our acquisition of Trustpage, as well as some exciting platform updates:
Vanta Names Security Leader David Eckstein As CFO
When is the right time for vulnerability scanning?
All it takes for cybercriminals to breach your mission-critical networks, database, and IT systems is a single unpatched vulnerability. To prevent this and maintain good cyber hygiene, you need to obtain real-time vulnerability data. Vulnerability scans generate a lot of data that when analyzed reveal several security flaws.