How Small Businesses Can Improve Their Cybersecurity
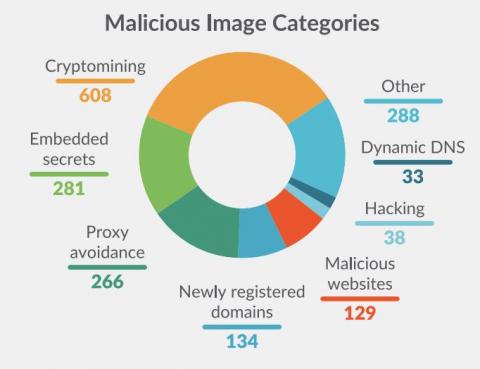
The need for cybersecurity in small and midsize businesses (SMBs) has never been more crucial. Any organization can suffer catastrophic effects from cyberattacks, but small businesses are particularly vulnerable. Unprepared small firms may experience tremendous financial consequences as well as damage to their reputation, productivity, staff morale and much more when a cyberattack occurs. When establishing cybersecurity processes and strategies, it is crucial to understand the risks.