Quantum computers vs. blockchain security: Racing against Q-Day
Image Source: depositphotos.com
Quantum computers have sprinted from science fiction to four-digit hardware. IBM’s Condor chip hit 1,121 qubits in December 2023, and rivals aren’t far behind. So what does that leap mean for the cryptography that protects your crypto wallet?
Every transaction you sign depends on public-key math—a shield Shor’s algorithm could eventually pierce. Wait too long for “Q-Day,” and attackers could rewrite blockchain ownership overnight. That’s why teams like Project 11 treat quantum risk as a problem for today, not tomorrow. The real-time “Q-Day Clock” maintained by Project 11 tracks how close we may be to a cryptanalytically relevant quantum computer, reminding the industry that quantum risk is a problem for today, not tomorrow.
What quantum computers threaten exactly

Quantum computing power is rapidly approaching the point where it can threaten today’s blockchain security.
Blockchains rely on two cryptographic pillars: public-key algorithms that prove you own an address and hash functions that lock data in place.
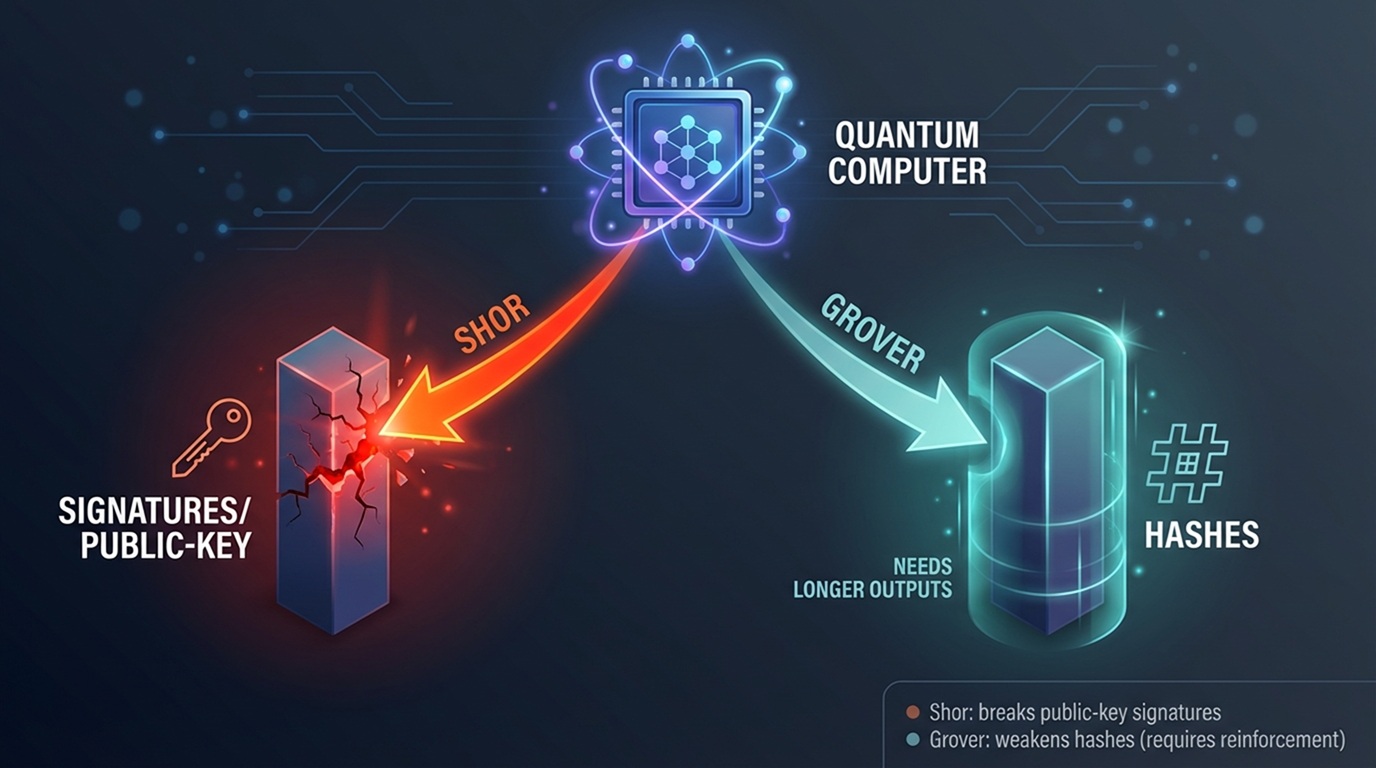
Shor’s algorithm directly threatens blockchain signatures, while Grover’s algorithm only weakens hash strength.
Shor’s algorithm gives quantum hardware a huge edge against public-key math. Recent studies estimate the break point anywhere from 20 million noisy qubits (to crack RSA-2048 in eight hours) to about 1,700 error-corrected qubits plus 2^36 Toffoli gates using a 2024 circuit optimization. Once a machine of that scale exists, an attacker could:
- Steal private keys from any address whose public key already sits on-chain and empty the wallet.
- Forge DAO votes or multisig approvals, shifting governance with a single fake signature.
- Seize upgrade paths that depend on legacy admin keys, halting migrations mid-flight.
Hashes hold up longer, but Grover’s algorithm still cuts brute-force complexity from 2^n to 2^{n/2}. That shift drops SHA-256’s pre-image strength from 256 to 128 bits. The fix is simple: double the output length or switch to a hash already sized for post-quantum safety.
Bottom line: signatures sound the fire alarm; hashes need thicker walls. Act early, and both can be reinforced before quantum hardware puts them to the test.
Why timing and “Q-Day” matter
Government schedules show the countdown has already begun, even if some teams still treat quantum risk as tomorrow’s problem. In May 2022 the White House issued National Security Memorandum-10, ordering every federal agency to start its post-quantum migration. NIST finalized three signature and key-exchange standards in August 2024 and added a fourth KEM in March 2025, with full FIPS publication planned for 2027. A June 2025 executive order set January 2, 2030 as the deadline for quantum-ready TLS in federal systems. The UK’s National Cyber Security Centre asks businesses to finish migrations before 2035 to avoid “last-minute chaos.”
These dates matter because quantum progress is uneven. A single leap in error correction or qubit fidelity can cut years off forecasts, and an attacker needs to succeed only once. When a cryptanalytically relevant quantum computer (CRQC) arrives, any on-chain public key becomes easy prey.
Blockchains face two extra hurdles:
- Changes to consensus rules often stretch across multi-year governance cycles.
- Historical data is public, so adversaries can “harvest now, decrypt later.”
Waiting for an exact Q-Day—whether 2030 or 2035—risks starting the migration after the window has closed. Act now, treat the standards timeline as a minimum, and plan several years of overlap between quantum-vulnerable and quantum-safe keys.
Three layers of quantum risk for blockchains
We picture quantum exposure as three concentric circles; each must be sealed before the next generation of hardware arrives.
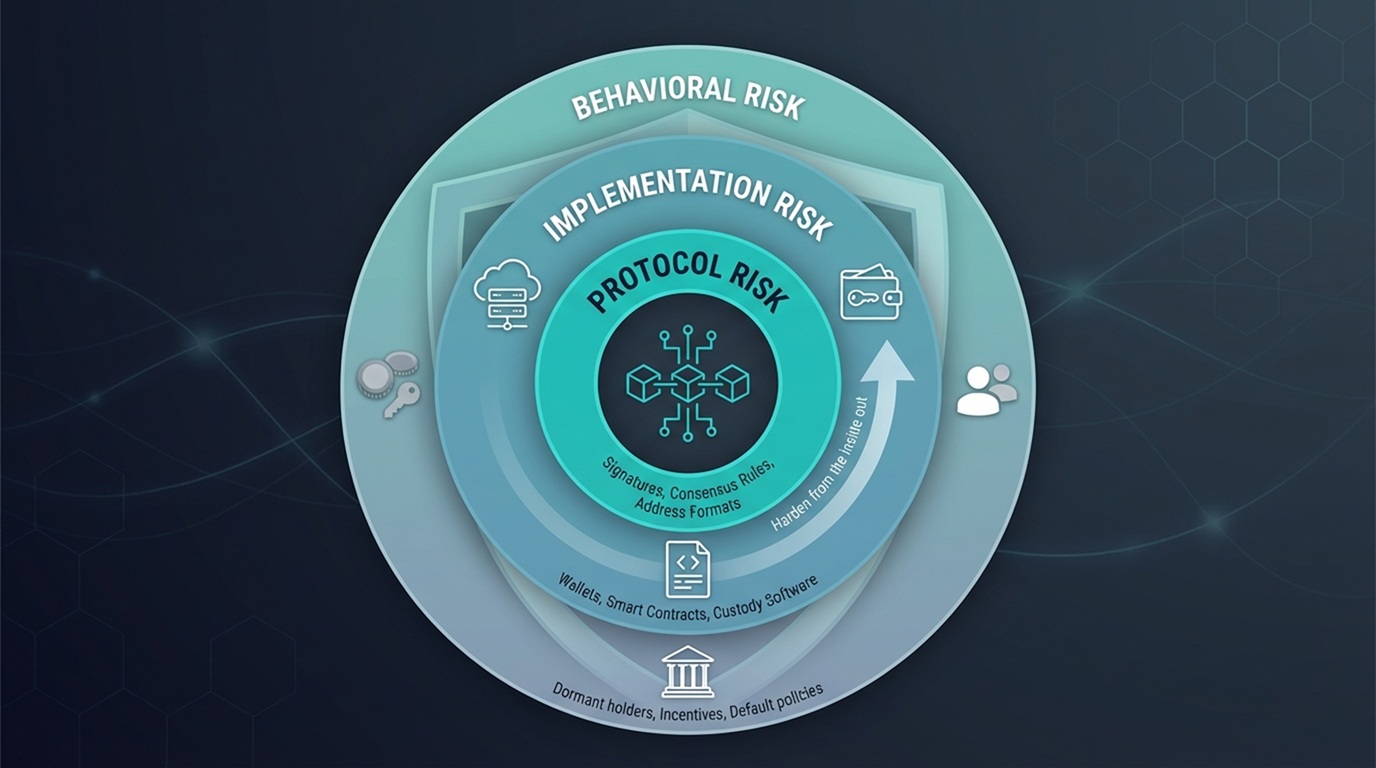
Quantum exposure spans protocol rules, software implementations, and the human behaviors that drive key migration.
- Protocol risk: the rules baked into consensus.
Bitcoin still signs transactions with ECDSA, and about 6.2 million BTC (roughly 29 percent of supply) sit in addresses whose public keys are already visible on-chain. A post-quantum hard or soft fork must replace those signature rules and introduce address types that hide keys until spend time. - Implementation risk: the software we run today.
According to a 2024 arXiv study, 7,852 deployed Ethereum contracts copied vulnerable code from Q&A sites. Wallets that reuse addresses, custodians that expose deposit keys, and upgrade paths locked behind legacy multisig give a quantum attacker easy entry even after the protocol strengthens. - Behavioral risk: the human factor.
According to Bitcoin Magazine, about one-third of Bitcoin holders never move their coins after the first transaction; any future migration will rely on nudging those long-dormant keys. Inventories, communications, and default-on incentives, such as blocking new sends to quantum-vulnerable scripts, close this final gap.
A strong defense starts from the inside out. We harden consensus, ship quantum-safe wallet workflows, and—most important—guide every user and institution through the move well before a cryptanalytically relevant quantum computer arrives.
What a specialized quantum-security lab focuses on
Picture a cross-disciplinary team where quantum physicists share a whiteboard with protocol engineers and game-theory economists. Labs like Project 11, along with peers such as PQShield (raised $37 million in Series B funding in June 2024) and QuSecure (won a $2 million U.S. Army contract in 2023), focus on three core jobs:
- Measure the blast radius. Engineers scrape block explorers and on-chain analytics to reveal how much value hides behind exposed public keys. One 2024 survey of Bitcoin UTXOs found that nearly 29 percent of the supply could be claimed if a cryptanalytically relevant quantum computer appeared tomorrow.
- Build the escape hatches. The team prototypes post-quantum address types, migration registries, and “move-your-coins” wizards so users can rotate keys with two clicks instead of twenty.
- Make it worth everyone’s while. Economists model fee rebates, airdrops, or staking boosts that nudge wallets and custodians to migrate early rather than in a panic.
Conclusion
The mission is practical, not alarmist: give you and the entire crypto ecosystem a clear, tested route to quantum safety before the hardware forces the issue.

