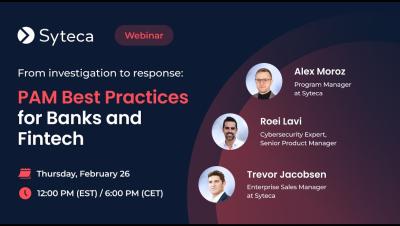
[Webinar] How to Detect Privileged Access Misuse Early | Syteca
Privileged accounts are one of the most common attack paths, yet misuse often goes unnoticed until serious damage is done. As identity becomes the new security perimeter, cybersecurity leaders face a growing challenge: privileged misuse often looks like normal administrative activity until real damage has already occurred. Watch this webinar to explore how organizations can move beyond traditional privileged access management and build an effective early detection strategy for privilege-based threats.