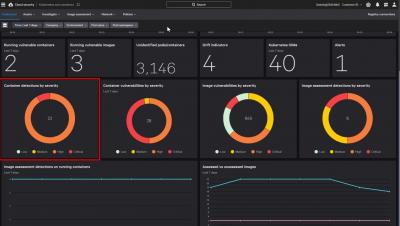
Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Identity is Key to Bolstering CI Controls
Tales from the Dark Web: How Tracking eCrime's Underground Economy Improves Defenses
Cybercriminals are constantly evolving their operations, the methods they use to breach an organization’s defenses and their tactics for monetizing their efforts. In the CrowdStrike 2022 Global Threat Report, we examined how the frequency and sophistication of ransomware attacks has grown in the past year.
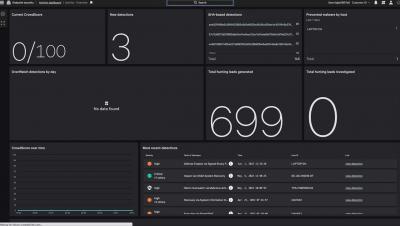
Falcon OverWatch Elite in Action: Tailored Threat Hunting Services Provide Individualized Care and Support
The threat presented by today’s adversaries is as pervasive as it is dangerous — eCrime and state-nexus actors alike are attempting to infiltrate companies and organizations of all sizes and across all verticals. While technology is a powerful tool for performing routine or repeatable analysis, the only way to effectively hunt and contain sophisticated and determined cyber threat actors is to use the expertise and ingenuity of human threat hunters.
Detecting and Mitigating NTLM Relay Attacks Targeting Microsoft Domain Controllers
Adversaries often exploit legacy protocols like Windows NTLM that unfortunately remain widely deployed despite known vulnerabilities. Previous CrowdStrike blog posts have covered critical vulnerabilities in NTLM that allow remote code execution and other NTLM attacks where attackers could exploit vulnerabilities to bypass MIC (Message Integrity Code) protection, session signing and EPA (Enhanced Protection for Authentication).
CrowdStrike Falcon Pro for Mac Achieves 100% Mac Malware Protection, Wins Fifth AV-Comparatives Approved Mac Security Product Award
CrowdStrike believes that continuous testing and evaluation by third-party organizations is critical in helping customers make informed decisions about which security solution best fits their needs. This is why CrowdStrike continues to participate in more third-party testing than any other next-gen endpoint cybersecurity vendor.
The Call Is Coming from Inside the House: CrowdStrike Identifies Novel Exploit in VOIP Appliance
CrowdStrike Services recently investigated a suspected ransomware intrusion attempt. The intrusion was quickly stopped through the customer’s efforts and those of the CrowdStrike Falcon Complete™ managed detection and response (MDR) team, which was supporting this customer’s environment.
EDR is the Path to XDR
CrowdStrike Falcon Stops Modern Identity-Based Attacks in Chrome
Recent research from CyberArk Labs presents a new technique for extracting sensitive data from the Chromium browser’s memory. However, existing access to the targeted system is required before leveraging the technique to extract the sensitive data. The technique could enable identity-based attacks involving authentication bypass using Oauth cookies that have already passed an MFA challenge.
Seven Key Ingredients of Incident Response to Reduce the Time and Cost of Recovery
When a breach occurs, time is of the essence. The decisions you make about whom to collaborate with and how to respond will determine how much impact the incident is going to have on your business operations.
For the Common Good: How to Compromise a Printer in Three Simple Steps
In August 2021, ZDI announced Pwn2Own Austin 2021, a security contest focusing on phones, printers, NAS devices and smart speakers, among other things. The Pwn2Own contest encourages security researchers to demonstrate remote zero-day exploits against a list of specified devices. If successful, the researchers are rewarded with a cash prize, and the leveraged vulnerabilities are responsibly disclosed to the respective vendors so they can improve the security of their products.
CrowdStrike Introduces CrowdStrike Asset Graph to Help Organizations Proactively Identify and Eliminate Blind Spots Across Attack Surface
CrowdStrike Adds Strategic Partners to CrowdXDR Alliance and Expands Falcon XDR Capabilities to Supercharge Threat Detection, Investigation, Response and Hunting
CrowdStrike Introduces Humio for Falcon, Redefining Threat Hunting with Unparalleled Scale and Speed
RSAC 2022: CrowdStrike Delivers Protection that Powers Productivity
The theme of RSA Conference 2022 succinctly captures the aftermath of the disruption we’ve all experienced over the last couple of years: Transform. Customers continue to transform and accelerate digital initiatives in response to the massive economic and technological shifts driven by the COVID-19 pandemic.
Detecting Poisoned Python Packages: CTX and PHPass
The software supply chain remains a weak link for an attacker to exploit and gain access to an organization. According to a report in 2021, supply chain attacks increased by 650%, and some of the attacks have received a lot of limelight, such as SUNBURST in 2020 and Dependency Confusion in 2021.
OverWatch Casts a Wide Net for Follina: Hunting Beyond the Proof of Concept
CVE-2022-30190, aka Follina, was published by @nao_sec on Twitter on May 27, 2022 — the start of Memorial Day weekend in the U.S. — highlighting once again the need for round-the-clock cybersecurity coverage. Threat hunting in particular is critical in these instances, as it provides organizations with the surge support needed to combat adversaries and thwart their objectives.
CrowdStrike Uncovers New MacOS Browser Hijacking Campaign
The CrowdStrike Content Research team recently analyzed a MacOS targeted browser hijacking campaign that modifies the user’s browsing experience to deliver ads. Research began with a variant that uses a combination of known techniques to deliver, persist and sideload a Chrome extension. Analysis of the fake Chrome installer uncovered the use of more than 40 unique dropper files to install the extension.
CrowdStrike Falcon Prevents the Follina Zero-day Vulnerability
CrowdStrike Falcon Identity Threat Protection Added to GovCloud-1 to Help Meet Government Mandates for Identity Security and Zero Trust
CrowdStrike recently announced the addition of Falcon Identity Threat Protection and Falcon Identity Threat Detection to its GovCloud-1 environment, making both available to U.S. public sector organizations that require Federal Risk and Authorization Management Program (FedRAMP) Moderate or Impact Level 4 (IL-4) authorization. This includes U.S. federal agencies, U.S. state and local governments and the Defense Industrial Base (DIB).
How CrowdStrike Achieves Lightning-Fast Machine Learning Model Training with TensorFlow and Rust
Supercharging CrowdStrike’s artificial intelligence requires both human professionals and the right technologies to deliver blisteringly fast and accurate machine learning model training with a small footprint on the CrowdStrike Falcon® sensor. CrowdStrike data scientists continuously explore theoretical and applied machine learning research to advance and set the industry standard in protecting customers from sophisticated threats and adversaries.