Sponsored Post
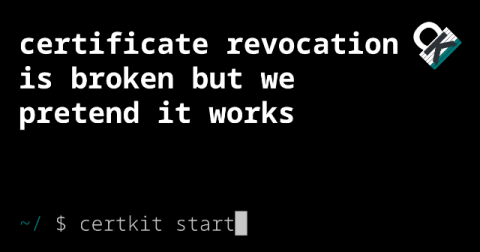
When Stripe's SSL Certificate Belonged to Someone Else
In 2010, Stripe bought stripe.com and started building the payment infrastructure that would eventually process billions of dollars. They bought their domain and ordered the SSL certificates. Except the previous owner of stripe.com still had a valid certificate. Valid for almost 2 more years.