What are CIS Benchmarks and how to use them?
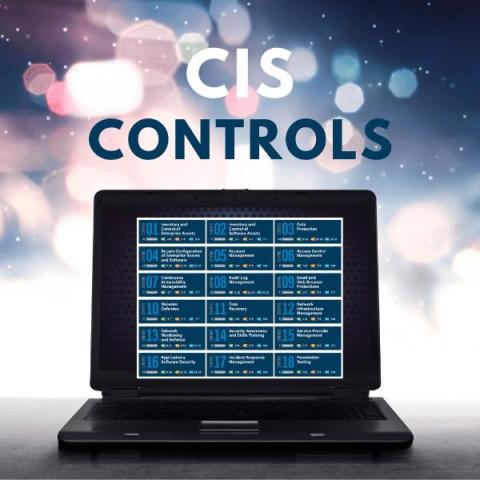
A list of 18 procedures (reduced from 20), or “controls,” recommended by the Center for Internet Security (CIS), must be followed to build an IT infrastructure resistant to cyberattacks. The CIS 4th Control advises to establish and maintain a secure configuration process for enterprise assets (end-user devices, including portable and mobile; non-computing/IoT devices; and servers) and software (operating systems and applications) (4.1).