Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
%term
RSA Conference 2019
The Safe (and Unsafe) Ways to Use Public Links for Collaboration
Earlier this week security firm Adversis published an article that exposed a vulnerability with a consumer-grade file sharing provider, which was created by the use of public links. For those who may not be familiar, many content collaboration solutions allow users to create links to one or more files or folders that can easily be shared internally or externally via text, email, social media, etc. (more info on links).
Higher Education Security Breaches To Learn From
Higher education finds itself facing a threat to its financial security even larger than student retention – data breaches. As colleges and universities begin to adopt mobile technologies, they also find themselves increasingly targeted by malicious actors. Understanding the recent security breaches impacting the industry can educate institutions about information security.
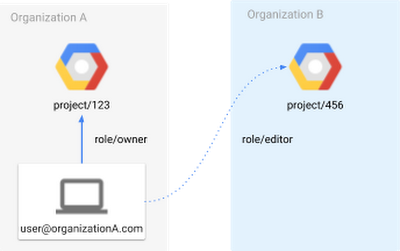
Help stop data leaks with the Forseti External Project Access Scanner
Editor’s note: This is the second post in a series about Forseti Security, an open-source security toolkit for Google Cloud Platform (GCP) environments . In our last post, ClearDATA told us about a serverless alternative to the usual way of deploying Forseti in a dedicated VM. In this post, we learn about Forseti’s new External Project Access Scanner. With data breaches or leaks a common headline, cloud data security is a constant concern for organizations today.
The Power of Vulnerability Management: Are You Maximizing Its Value?
Tripwire has been in the business of providing vulnerability management solutions with IP360 for about 20 years. With over 20,000 vulnerabilities discovered last year alone, vulnerability management continues to be an important part of most security plans. And most organizations agree.
Understanding Vulnerability Scoring to Help Measure Risk
Understanding vulnerability scoring can be a daunting task, but a good starting point is first understanding risk and being able to distinguish risk from a vulnerability. Both have been used interchangeably throughout the years. A vulnerability is some aspect of a systems functioning, configuration or architecture that makes the resource a target of potential misuse, exploitation or denial of service.
What's better: On-site SIEM or MSSP SIEM?
If an organization properly implements a SIEM solution, it efficiently draws attention towards warning signs as well as suspicious activity within the network. With the ever-evolving cyber space, continuous security monitoring has become exceedingly important. The benefits of SIEM also extend to understanding business and technology environments, monitoring availability and performance, issue diagnosis, and creation of a report on network activities.
How to Ensure Network Security?
With a colossal surge in cyber-attacks and high reliance on technology in this digital age, ensuring the security of data and information have become a daunting task. Cyber threats are accelerating significantly even faster than the enhancements businesses are making. Computer networks have become bigger and their interconnectivity using a Wide Area Network (WAN) is worldwide due to globalization.