Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
%term
What is API Security Testing & How to Perform It? A Detailed Guide
What is API Security Testing? API security testing is a process of carefully evaluating API endpoints to identify and remediate vulnerabilities such as fuzzy input, parameter tampering, or injection attacks. Acting as the first line of defense, it meticulously examines endpoints to identify and neutralize vulnerabilities before attackers can exploit them.
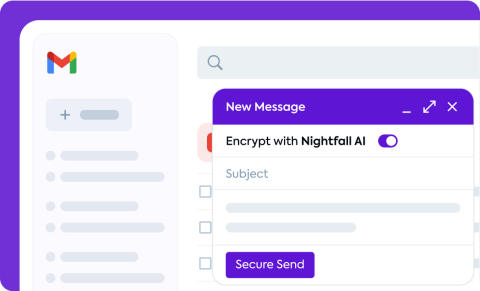
How to Send Encrypted Emails in Gmail in 5 Easy Steps
In today's digital landscape, email encryption is a key component of data protection, especially for organizations that handle personal, financial, or health-related information. Whether you need to safeguard Personally identifiable information (PII), Payment card data (PCI), Protected Health Information (PHI), secrets, or Intellectual Property (IP), this guide will walk you through the process of sending encrypted emails in Gmail.
Top 10 EdTech Blogs and Trends to Follow in 2024
The world of education technology (EdTech) is constantly evolving, with new tools, platforms, and approaches emerging every year. As an educator or EdTech enthusiast, staying up-to-date with the latest trends and insights is crucial for making informed decisions and providing the best learning experiences for students. From Virtual Team Development Games to immersive simulations, gamification can engage students and make learning more fun and interactive. In this article, I've curated a list of the top 10 EdTech blogs and trends to follow in 2024.
The Power of Combining a Modular Security Data Lake with an XDR
The 2024 Global Digital Trust Insights survey from PwC reports that 36% of businesses have experienced a data breach that cost more than $1 million to remediate. Cyber threats are clearly on the rise and in today’s volatile threat environment, it is a matter of when - not if - a cybersecurity incident will occur. Digital adversaries are becoming more sophisticated and relying on weak links to exploit company applications and infrastructure.
Ransomware in the Global Healthcare Industry
The World Health Organisation (The WHO) hosted a webinar on the 18th of July to discuss the critical importance of cybersecurity in the healthcare sector, highlighting the severity of the situation the industry is currently facing. Healthcare organisations are increasingly relying on digital systems to facilitate their daily workflow, but the prevalence of outdated legacy technology in the sector is rendering it vulnerable to cyber-attacks with severe consequences.
[miniOrange Webinar] Zero Trust and IAM: Building a Secure Future
This video features our exclusive miniOrange webinar on Zero Trust and IAM: Building a Secure Future. Our cybersecurity experts explain how to set up a Zero Trust security network with key components like IAM, PAM, CASB, DLP, and MDM. Together, these components create a comprehensive security strategy that safeguards sensitive data and IT resources. Witness live demonstrations of Zero Trust solutions in action, showcasing their unique features and deployment options.
Turning Novel Threats into Detections Easily with SnapAttack
Our CTO, Fred Frey, met with Teddy Powers from Google Cloud Security at the Google Massachusetts Ave Office to discuss the topic: "Turning Novel Threats into Detections Easily with SnapAttack." Discover how SnapAttack can integrate with Mandiant's threat intelligence, security validation, and Google Chronicle to enhance detection and create actionable workflows for your organization.
Strengthen Your Cyber Defense with Microsoft Copilot for Security
Discover how to unleash the full capabilities of your Microsoft Security tools and optimize your Copilot experience with BlueVoyant.
Get Ready for NIS2 with BlueVoyant
Identify gaps and achieve NIS2 readiness with BlueVoyant.