How to secure Syslog with USM Anywhere
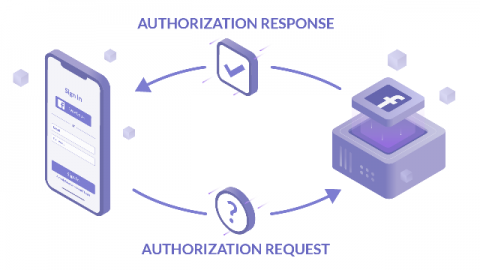
One of the requests we often get is how to securely forward logs to the USM sensor. To forward logs securely, the one component that is required is an SSL certificate. By default, USM has a self-signed certificate that will allow sending secure logs over port 6514. Some platforms, such as Palo Alto Networks, require publicly signed certificates by default. In this blog, we will walk through the process of generating a publicly signed certificate for use with USM.