Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Threat Detection
Discovering and Blocking a Zero-Day Exploit with CrowdStrike Falcon Complete: The Case of CVE-2023-36874
CrowdStrike Counter Adversary Operations is committed to analyzing active exploitation campaigns and detecting and blocking zero-days to protect our customers. In July 2023, the CrowdStrike Falcon® Complete managed detection and response (MDR) team discovered an unknown exploit kit leveraging a still-unknown vulnerability affecting the Windows Error Reporting (WER) component.
Mind the (Interpretation) gap: Another reason why threat modeling is important
Where do vulnerabilities fit with respect to security standards and guidelines? Was it a coverage issue or an interpretation and implementation issue? Where does a product, environment, organization, or business vertical fail the most in terms of standards requirements? These questions are usually left unanswered because of the gap between standards or regulations on the one hand, and requirements interpretation and implementation, on the other.
Enhance Threat Detection and Response with Intel DNS
ThreatQuotient and Infoblox recently hosted a webinar, where they demonstrated how the combination of DNS Intel and the use of a Threat Intelligence Platform (TIP) help to improve threat detection and response capabilities. Infoblox specializes in DNS Intelligence where their internal experts analyze, process and qualify DNS intelligence (analyzing around 70 billion DNS requests). The results of these analyses provide customers with an enriched, qualified and reliable source of information.
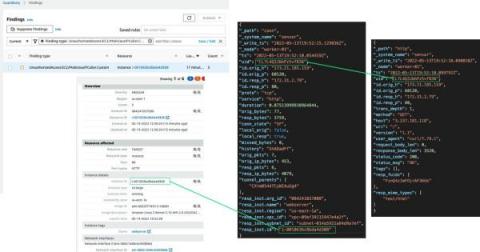
Detections and Findings using Corelight in the Black Hat Asia NOC
As promised, we wanted to dedicate a blog to detections and findings from the network operations center (NOC) at Black Hat Asia 2023 as a follow up to our Lessons Learned blog. Some of these discoveries may not surprise the seasoned analyst or senior threat hunter – but will hopefully provide a little entertainment, because the more things change, the more they stay the same.
Detecting Storm-0558 using Corelight evidence
While there have been many intrusions, compromises, breaches, and incidents that have made news in the IT and InfoSec industries throughout 2022 and into this year, when events or threats like Storm-0558 gain coverage by mainstream media, we often get questions about Corelight’s ability to detect threats through our sensors, products & platform.
Cloudflare Radar's new BGP origin hijack detection system
Border Gateway Protocol (BGP) is the de facto inter-domain routing protocol used on the Internet. It enables networks and organizations to exchange reachability information for blocks of IP addresses (IP prefixes) among each other, thus allowing routers across the Internet to forward traffic to its destination. BGP was designed with the assumption that networks do not intentionally propagate falsified information, but unfortunately that’s not a valid assumption on today’s Internet.
Comprehensive visibility is the foundation for effective threat detection and response
Businesses today are more dependent than ever on technology, making strong threat detection and response strategies essential. Cybercriminals in the modern world are constantly looking for new and creative ways to hack into organizational networks and steal sensitive data. Comprehensive visibility is a crucial element that is sometimes paid less attention to yet is the foundation of efficient threat detection and reaction.
I have trust issues and so does my CISO
Trust is hard to earn but necessary for any successful relationship. As organizations build the systems to support Zero Trust, they find themselves balancing security and functionality across their operations. Incident Response and Network Operations in particular can be full of traumatic experiences, and as we sink into those moments the typical responses are freeze, flight, or fight.