Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
%term
What is Access Control? Components and Types
Digital transformation changes the perimeter. When organizations had all their applications on-premises, the network firewall kept the right users inside the gate and malicious actors outside. However, the move to the cloud changed all that. In today’s hyper-connected ecosystem, understanding the components and types of access control can help you strengthen security.
Top vulnerability assessment and management best practices
By implementing these vulnerability assessment and vulnerability management best practices you will reduce the attack surface of your infrastructure. We’re human, and many things we build aren’t perfect. That’s why we take our cars for a periodic inspection, or why we have organizations certifying that products are safe to use. Software is no different.
Vulnerability Management with Sysdig
The SASE Solution to Network and Security's Complicated Relationship Status
If our friends Security and Networking were on Facebook, they would probably both list their relationship status as “It’s Complicated.” Sometimes everything’s great, but now and then things can get a little weird, unclear, or uncomfortable. At many organizations, there has traditionally been a barrier between the security and networking teams. Each team has its own objectives — and at times, those objectives can be at cross-purposes.
Essential Eight Compliance Guide (Updated for 2021)
In an effort to significantly improve the cyber resilience of Australian businesses, the Australian federal government is mandating compliance across all eight cybersecurity controls of the Essential Eight framework. This is an ambitious move that may be burdensome to the many entities still struggling to comply with just the top four controls of the Essential Eight.
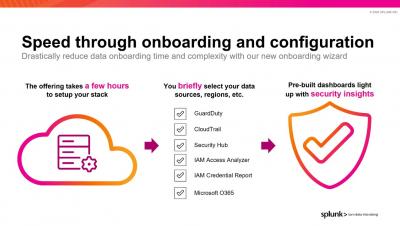
Detecting and Investigating Threats in Splunk Security Analytics for AWS
SOCtails Episode 4 - Respond Fast to Security Incidents with Automated Playbooks
Announcing State of Software Security v11: Open Source Edition
Today, we published the open source edition of our annual State of Software Security report. Solely focused on the security of open source libraries, the report includes analysis of 13 million scans of more than 86,000 repositories, containing more than 301,000 unique libraries. In last year’s open source edition report, we looked at a snapshot of open source library use and security.
How to Interpret the Various Sections of the Cybersecurity Executive Order
The Biden administration released a new executive order for cybersecurity on May 12, 2021. Although many know the overarching message of the executive order, it’s also important to know the specific details outlined in each section.