Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest News
Application Security Requirements: Trends and Best Practices
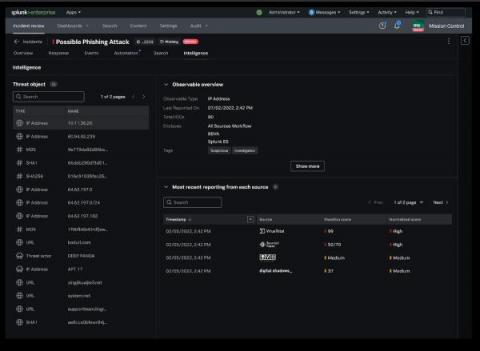
Integrated Intelligence Enrichment With Threat Intelligence Management
What Does a Password Manager Do?
A password manager stores passwords securely, generates strong passwords, identifies weak and reused passwords, generates and stores 2FA codes, and stores other sensitive data like important files. Read on to learn more about what password managers do and why investing in a password manager is worth it.
The Rekt Test: 12 Questions to Assess Your Blockchain Security
At Fireblocks, we firmly believe that industry collaboration and intelligence-sharing drives adoption of the best security practices and advances the ecosystem as a whole. This week, Fireblocks, along with fellow Web3 cybersecurity leaders, released the Rekt Test, a simple yet powerful guide for any business to test and assess the security of their blockchain application.
Multiple Junos OS Vulnerabilities Could lead to Unauthenticated Remote Code Execution
How to Build a Risk Register for Your Business
Checklist for Third-Party Risk Assessments
What are the Principles of Information Security?
Tennessee Employees Lose Their Data to Consolidated Retirement System Breach
The Tennessee Consolidated Retirement System is a retirement and benefits program administered to many full-time employees throughout the state. If you are an employee within the state of Tennessee, there's a good chance that your data is tied up in this system and that you're relying on the program administrators to protect your personal and financial information.